Last updated on April 14th, 2024 at 08:48 pm.
Ubuntu 22.04 Initial Server setup on a VPS like Vultr, DigitalOcean, Linode, hetzner, Contabo etc
In this post you’ll deploy an Ubuntu 22.04 Vultr VPS server and then do an Ubuntu 22.04 initial server setup to make it ready for production. These are the minimum steps you need to take before using your server in a production environment. This post will cover Ubuntu 22.04 Initial server setup using a Vultr instance. However, you may use this same guide to set up Debian 10/11 and Ubuntu 20.04.
You can follow along on a Mac / Linux using Terminal.
On a Windows PC, follow along with Git Bash. You can do this Ubuntu 22.04 initial server setup on Windows using Git Bash.
What we’ll do in this Ubuntu 22.04 Initial Server setup
The following are the steps we’ll take to set up our Ubuntu VPS server.
Feel free to skip to the different sections of this server setup guide using the links below.
Step 1 : Deploy Ubuntu 22.04 Vultr server
Step 2 : Log in via SSH
Step 3 : Ubuntu 22.04 Create user + Ubuntu 22.04 add user to sudoers
Step 4 : Ubuntu 22.04 SSH Key Login Set up
Step 5 : Disable root login and Password Authentication
Step 6 : Ubuntu 22.04 Firewall Setup
Step 7 : Ubuntu 22.04 Change SSH Port
Step 8 : Create a swap file
Step 9 : Change Server Hostname
Step 10 : Set Timezone
Step 11 : Setup Automatic Updates
Step 12 Install HestiaCP Ubuntu 22.04
Step 1 : Deploy Ubuntu 22.04 Vultr server
First, you need to head over to Vultr to deploy a server. Here is $100 Vultr Credit to get started with.
Go to Vultr and create an account. Once you are on the Vultr dashboard, follow the steps in this post to install your Ubuntu 22.04 server.
Step 2 : Log in via SSH
In this setup, you can use Terminal or Git Bash. If you are on a Mac or Linux, just open up the terminal window and start following along.
If you are on Windows, download Git Bash and install it from git-scm.com. Download and install the full Git software. Open the Windows start menu, search for Git Bash and open it.
Logging into Ubuntu VPS with SSH using Git Bash or Terminal
You need your Ubuntu user, password and IP to log in remotely using SSH. All these details are provided on your Vultr dashboard.
Open up terminal or Git Bash.
Type in the following and then enter your password:
ssh user@server-ip-address
Let’s break it down for you if you are a beginner.
User – This is the username for your Ubuntu server. By default, it is root. You will get this info in your email. Default Vultr Ubuntu 22.04 user is root.
Server-ip-address – The IP address of your server will be shown on your dashboard next to your instance.
If your username is root and IP as 127.0.0.1, you will log in as follows:
ssh [email protected]
Then type in your password which can be copied from your dashboard. When typing in or pasting your password, it will be hidden. You won;t see any characters as you type it.
After you log in , update your server.
sudo apt update && sudo apt upgrade -y
I will be using Vim in this guide. If you are on a minimal installation of Debian or certain Ubuntu VPSes, you will need to install Vim.
sudo apt install vim
If you do not want to use Vim, wherever I have used vi, just replace it with nano.
#instead of sudo vi filename #do sudo nano filename
Step 3 : Ubuntu 22.04 Create user + Ubuntu 22.04 add user to sudoers
After logging in and updating your Ubuntu server as shown in step 2 above, let us create a new Ubuntu user and add the user to the sudoers group.
Why create user and add user to sudoers group in your Ubuntu server?
This is because everybody that uses a Linux server knows that root is the default user in almost all Linux distros. Therefore, for better security, you need to create a unique user. At some point later on, we’ll see how to disable the root user from logging into our server via SSH.
Ubuntu 22.04 Create user
Create an Ubuntu user via the Command line as follows. Remember to change the username from thenewuser to any unique username you can remember later.
adduser thenewuser
Then create a secure password for your user.
You will be asked certain details about the user, you can press enter to keep skipping these details.
Most importantly, ensure you give your user a name and password that you can remember when you need to ssh into your VPS. Save them somewhere safe for reference.
Ubuntu 22.04 add user to sudoers
After creating your new user, you need to add them to the sudoers group so that they do admin level tasks on your server.
The new user will need the keyword sudo to do admin level stuff on your server.
Add user to sudoers group as follows:
usermod -aG sudo thenewuser
If you experience an error where sudo is not recognized, check out step 3 in this Linux server setup post.
Open up a new instance of Git Bash or terminal and log in with the new user:
ssh [email protected]
Enter the password you created for the new sudo user.
Then try running a sudo command to see if they were successfully added to the Ubuntu sudoers group.
sudo apt update
If you receive an error, then try adding the user to the sudo group again or install sudo and try again.
If you receive a prompt telling you to be mindful of others and act responsibly because of your new powers, then you have created an Ubuntu 22.04 user and added them to the sudoers group.
Stay logged in as the new sudo user . The next steps will be done as the new sudo user.
Step 4 : Ubuntu 22.04 SSH Key Login Set up
The next step in this Ubuntu 22.04 initial server set up is to enable SSH key authentication / SSH Key login.
In this part, I will be using Git Bash, if you are on a Mac or Linux you can still follow along. However I would suggest you look at my original SSH Key Login setup for Linux. Use the second method to set up your Key. Everything is well explained and laid out in that post.
The point of generating SSH keys and adding them to the server is to log in using public key authentication, whereby you won’t need to log in with a user password. With public key authentication you just need your private key to log in once you have added the public key to your server.
Let’s see how to set this up.
You may use the following part to set up public key authentication for Debian, CentOS, RHEL,Almalinux, RockyLinux and of course Ubuntu. Try other Linux server OSes, it should work too.
Let’s set up SSH key login for Ubuntu 22.04
The next phase in this Ubuntu 22.04 initial server setup will be:
- generating the SSH key pair,
- adding the public key to the server
- and testing our login with the SSH key pair.
Note: I will be using Git Bash on Windows.
SSH Keygen – Windows with Git Bash
When you install Git. it comes with Git Bash.
On Windows after running Git Bash if you go to your User’s home directory ( C:\Users\{username} ), you will find the .ssh folder. This is where we’ll store our generated SSH keys.
i) Create a folder for your key pair
We’ll store the SSH keys in a folder like this – C:\Users\username\.ssh\sshkeyfolder.
So, head over to your .ssh folder in Windows and create a folder for your key pair. In my case it is called sshkeyfolder.
The benefit of doing this is that you can put different keys for different servers/users in different folders so that you don’t overwrite your keys.
ii) SSH keygen on Git Bash
This is done on your local computer. Ensure you are not logged into your server when running the ssh keygen command.
Enter the following with the details you want for your key. Then press enter. That will generate your key pair in a folder inside of the .ssh folder ; a folder called sshkeyfolder.
And the name of your key will be VultrUbuntu2004serverkey_rsa.
ssh-keygen -t rsa -b 4096 -f ~/.ssh/sshkeyfolder/VultrUbuntu2004serverkey_rsa
The tilde (~) is a shortcut for your home directory, in my case it is short for C:\Users\username\ .
My keys will be named VultrUbuntu2004serverkey_rsa. You can name yours however you wish. Examples of names : key1, keyforUbuntu2004, keyid_rsa
You can add various flags as you generate the key. We used -t, -b, -f which are explained below.
-t – this specifies the type of key. It specifies the algorithm of the key. The algorithms available are rsa, ecdsa, ed25519 .The ecdsa and ed25519 algorithms are more modern. I chose rsa of 4096 bits because it is widely supported by almost all SSH clients and OSes.
-b – This specifies the size of the key. For an rsa key you should either use 2048 bits or better yet, 4096 bits.
-f – This flag specifies the filename. Enter the full absolute path.
You can read more SSH options here.
You may choose to add a passphrase as an extra security for your key. Enter passphrase then press enter.
Your 2 SSH keys will be generated and stored in the folder you specified. In my case they will be in C:\Users\username\.ssh\sshkeyfolder.
Public ssh key vs private.
The public ssh key has an extension of .pub. The private key has no extension. The public key is the one that will be added to your server. The private key will remain on your computer and be used for SSH login authentication.
In my example, the private key will be named as VultrUbuntu2004serverkey_rsa. And the public key will be named as VultrUbuntu2004serverkey_rsa.pub .
ii) Public SSH key Ubuntu 22.04 Upload
Next step is to add the public key to the Ubuntu 22.04 server. You are still not logging into your server yet. This is done on GitBash while you are logged out since your keys are actually on your local PC.
The path for my public key is : ~/.ssh/sshkeyfolder/VultrUbuntu2004serverkey_rsa.pub .
In order to add it onto my server, I will just do the following and then enter the password for the user :
ssh-copy-id -i ~/path-to-public-key user@host
That is:
-i is the identity of the public key. Give the absolute path of the public key. In my example it will be, ~/.ssh/sshkeyfolder/VultrUbuntu2004serverkey_rsa.pub .
User is the Ubuntu sudo user you created above in step 3.
Host is your Ubuntu server IP address.
If my Ubuntu sudo user is thenewuser and my server IP address is 127.0.0.1, I will add the public SSH key as follows:
ssh-copy-id -i ~/.ssh/sshkeyfolder/VultrUbuntu2004serverkey_rsa.pub [email protected]
You will then need to enter a password for the user and the key will be added to the authorized_keys file on your server.
Permissions for the authorized_keys file and the .ssh folder will be set appropriately by the ssh-copy-id function.
That’s it for copying the keys to your server. If everything goes well, just skip over to step 5 Disable root login .
If not, continue as advised below.
Experienced ssh-copy-id error ?
If you experience any issue whereby you cannot use ssh-copy-id, you can copy and paste the keys manually into the authorized_keys file in your server.
Open and edit the SSH key file. Go to your .ssh folder on your local computer and open the file with .pub extension using any text editor like VS Code. Copy everything in there.
Create the .ssh folder and authorized key as below. Then paste in the public key. Ensure it is all in one line, not multi-lines.
sudo mkdir ~/.ssh; sudo nano ~/.ssh/authorized_keys
When you copy the public key to your server manually, ensure you update the keys permissions . If you don’t, Linux will not let you log in with the key pair.
sudo chmod 700 -R ~/.ssh && sudo chmod 600 ~/.ssh/authorized_keys
Then finally, this is very important. Change ownership to the user you are creating the SSH login for. Without doing this you won’t be able to log back in by SSH keys.
Then change ownership to your new user’s Folder …
sudo chown -R thenewuser:thenewuser /home/thenewuser
Ubuntu login with SSH Key
Next up try to log into your server with your SSH private key. We’ll try to log into Ubuntu with the SSH key.
ssh user@server_ip -i ~/.ssh/path-to-private-key
Example login using the SSH key:
ssh [email protected] -i ~/.ssh/sshkeyfolder/VultrUbuntu2004serverkey_rsa
To log in, you need to use the private key. The private key is the one without an extension. The public key has a .pub extension.
Step 5 : Disable root login and Password Authentication
After ascertaining that you can log in using your private key, then you need to disable root login and password Authentication.
The root user will not be able to SSH into your Ubuntu server after this. And logging into the server will only be possible using password authentication.
We can achieve both by editing the SSH config file which is located at /etc/ssh/sshd_config.
Edit it using vim or nano. Here is a quick vim tutorial for beginners.
sudo vi /etc/ssh/sshd_config
Look for the PermitRootLogin line, uncomment it (remove the #) and set the value to no.
PermitRootLogin no
Do the same for the PasswordAuthentication line:
PasswordAuthentication no
Save and close the file.
Saving and closing in VIM:
- :q! – Force quit without saving the changes .
- :wq – Save and quit .
To apply the new settings, reload SSH.
On RHEL based OS:
sudo systemctl reload sshd
Debian / ubuntu: Use either
sudo service ssh restart sudo systemctl restart ssh
Open up a new instance of Git Bash and try to log in as root. It should refuse.
Also try to log in with the password. It wont let you.
Most importantly open a new Git bash or terminal window and try to log in with the correct key and user to ensure that you did not mess anything up. Ensure you can log in successfully before closing the window where you are logged in .
Step 6 : Ubuntu 22.04 Firewall Setup
If you will not be installing a Control Panel that will set up the firewall rules for you, then you can use Uncomplicated Firewall(UFW) to set up Ubuntu 22.04 firewall.
Install UFW Ubuntu 22.04
Install UFW on your VPS. It is probably already installed
sudo apt install ufw
Activate UFW
Enable UFW :
sudo ufw enable
UFW rules setup
Allow SSH or you will be locked out of your server
sudo ufw allow ssh
You can also allow rules using the port like this:
sudo ufw allow 22/tcp
After changing the SSH port in step 6, allow the new port.
By default allow outgoing and deny incoming traffic. This is good because it lets you explicitly only allow the incoming traffic you choose.
sudo ufw default allow outgoing sudo ufw default deny incoming
Then allow various important traffic such as SSH
sudo ufw allow ssh
Or allow the new SSH port if you change it.
sudo ufw allow 7059
You can check and edit your ufw default configuration in /etc/default/ufw .
sudo vi /etc/default/ufw
The following part is extracted from part 4 of this Ubuntu 20.04 setup .
Check the status of ufw :
sudo ufw status
If it is inactive ,activate it :
sudo ufw enable
You may also disable it:
sudo ufw disable
You can allow various services.
Definitely allow SSH. or you won’t be able to log into your server.
sudo ufw allow ssh
You can allow a specific port through your firewall;
sudo ufw allow 2003
Block all incoming traffic and allow http and https afterwards :
sudo ufw default deny incoming
Allow HTTP and HTTPS traffic;
sudo ufw allow http sudo ufw allow https
To enable UFW after setting the rules :
sudo ufw enable
You can delete rules based on their numbers.
First list all the rules based on the numbering ;
sudo ufw status numbered
Look at the number of the rule and delete it. Below will delete rule 5 on the firewall rules.
sudo ufw delete 5
Check if UFW is active and running:
sudo ufw status verbose
You will get a status of active or inactive.
You can deny any connections as well. Close out any ports that are not being used or are being misused. Eg deny outgoing mail:
sudo ufw deny out 25
You can reset all the UFW firewall rules as follows
sudo ufw reset
There are no specific rules for your firewall. Just enable the items you need to enable and disable any traffic you don’t need.
Step 7 : Ubuntu 22.04 Change SSH Port
You can use any port number from 1 to 65535 as long as the port is free and not being used by another service.
Edit the port number in the SSH configuration file.
If you don’t know how to use vim, you can use the nano editor as follows:
sudo nano /etc/ssh/sshd_config
Or use Vim. Learn to use Vim here quickly.
sudo vi /etc/ssh/sshd_config
I will change the Port number to 7059. Change yours to any number you prefer. Ensure it is a free port not being used by any other service.
Port 7059
If Port is commented , uncomment it by removing the # sign.
Save and exit the file.
On nano save and exit by doing CTRL X, then press Y , then Enter.
On Vim save by typing :wq or do Shift ZZ .
Then restart SSH :
sudo service ssh restart
Or
sudo systemctl restart ssh
Then add the new port to your Ubuntu 22.04 Firewall using ufw:
ufw allow 7059
Replace 7059 with your port number.
Open up a new Git Bash window and try to log in with the new port as follows:
ssh user@server_ip -i ~/.ssh/path-to-private-key -p PortNumber
Example:
ssh [email protected] -i ~/.ssh/sshkeyfolder/VultrUbuntu2004serverkey_rsa -p 7059
If you can log in then that’s perfect. Your port has been changed successfully.
Step 8 : Create a swap file
A swap file is useful if you have low memory on your VPS.
Let’s see how to create an Ubuntu 22.04 swap file .
I’ll skip over irrelevant steps and just show the actual steps for creating the swap file,
Step 1 : Create the swap file and give it any name you prefer.
I’m creating a file named myUbuntuSwapfile. I am allocating 2Gb, you can allocate more depending on your total RAM.
sudo fallocate -l 2G /myUbuntuSwapfile
Step 2 : Give the file a more restrictive permission
sudo chmod 600 /myUbuntuSwapfile
Step 3: Convert the created file to a swap file (mkswap) and then activate it (swapon).
sudo mkswap /myUbuntuSwapfile && sudo swapon /myUbuntuSwapfile
Step 4 : Persist the swap location even when the system restarts. Do this by adding it to /etc/fstab .
You can edit using nano but I will use Vim.
sudo vi /etc/fstab
Add the swap file in the last line of /etc/fstab as follows
/myUbuntuSwapfile swap swap defaults 0 0
Save and exit (Esc , then :wq )
Step 5 : Check if our swap file is now available.
Important Note: My website is stripping out double hyphens, so type in the command as shown in the screenshot below:
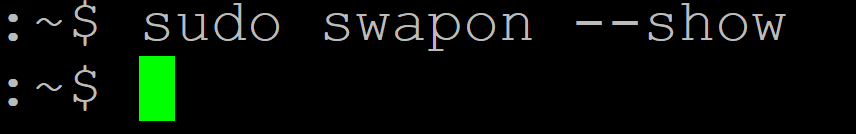
sudo swapon --show
Then confirm the available memory on your VPS. The new swap memory should be included in the list.
sudo free -h
Step 9 : Change Server Hostname
On Vultr this process should be optional since you can set the hostname for your Ubuntu server when deploying the server .
Set your Ubuntu server hostname as follows.
sudo hostnamectl set-hostname subdomain.example.com
Replace subdomain.example.com with the hostname of your choice. Use a fully qualified domain or subdomain if you will be sending mail from the server.
Next step is to change the hosts file.
Edit the hosts file – /etc/hosts .
sudo nano /etc/hosts
Change the old name to the new one in the hosts file.
Restart the server :
shutdown -r
or
reboot
You can also change the server hostname manually.
Step 10 : Set Timezone
On your Ubuntu 22.04 VPS you may want to set the timezone to your location.
Use tzdata to select your timezone :
sudo dpkg-reconfigure tzdata
Select your Continent, then City. Then press enter.
Step 11 : Setup Automatic Updates
To achieve automatic Ubuntu 22.04 updates we’ll use the unattended-upgrades package.
Step 1 : Update your server and Install the unattended-upgrades package and activate it.
sudo apt update && sudo apt upgrade -y sudo apt install unattended-upgrades
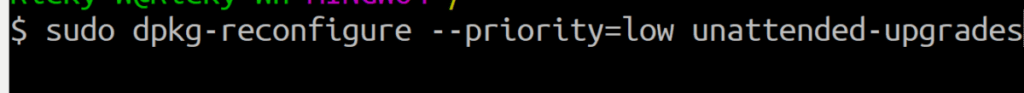
Step 1.1 Enable automatic updates in order to generate the files you need to customize. Run the following and select yes.
sudo dpkg-reconfigure --priority=low unattended-upgrades
My front-end is stripping out double hyphens, so type the above with double hyphens. Specifically double hyphen priority=low. Shown in the screenshot below.
On Debian also add :
sudo apt install apt-listchanges
Step 1.2 : To enable auto reboot and notifications, you also need to have the update-notifier-common package. On minimal Ubuntu installs, you need to install it as so:
sudo apt install update-notifier-common
Step 2 : The next step is to configure what you need to be updated in the 50unattended-upgrades file. Open it with Nano or Vim.
sudo vi /etc/apt/apt.conf.d/50unattended-upgrades
By default 50unattended-upgrades looks like the screenshot below. If you scroll down the file you will see that there are more options you can change. They are all commented for your understanding:
You can see that only security updates are enabled by default.
Step 2.1 : You can enable package updates by uncommenting the lines within the red highlighted area. For instance uncomment package updates by removing the preceding double slashes (//) as shown below:
"${distro_id}:${distro_codename}-updates";Step 2.2 : Since you have enabled package updates, there may be packages you want to hold updates for. Any package you don’t want to update can be explicitly defined in the blacklist area .
Perhaps you do not want to update php8.0 and nginx.
Anything you do not want updated, add it within the curly brackets of this line
Unattended-Upgrade::Package-Blacklist {
"php";
"Nginx";
"mariadb";
// The following matches all packages starting with linux-
// "linux-";
Step 3 : Enable notifications and reboot.
This is optional. If you need notifications or you need to reboot the server post updates, you can set this up in the 50unattended-upgrades file.
sudo vi /etc/apt/apt.conf.d/50unattended-upgrades
Step 3.1: Enable email notifications.
For email notifications to work your server needs a working mail server setup.
To enable email notifications, scroll down to this line :
in vim you can search by pressing esc, then type this /Unattended-Upgrade::Mail . Then press enter and use n and N to navigate up and down. Press i to edit.
//Unattended-Upgrade::Mail " ";
Uncomment it by removing the double slashes, then enter a working email as follows.
Unattended-Upgrade::Mail "";
Step 3.2 : Enable reboot
You can also enable reboots after updating. Locate the lines below and uncomment them, then update them accordingly. The final edits should be as shown below.
Unattended-Upgrade::Automatic-Reboot "true";
You can set a specific time for the reboot based on the 24hour clock system.
//reboot happens at 1 am. Unattended-Upgrade::Automatic-Reboot-Time "01:00"
Finally check status
Check the status of autoupdates like this:
sudo apt-config dump APT::Periodic::Unattended-Upgrade
If the result is as shown below then Ubuntu 22.04 autoupdates is turned on.
APT::Periodic::Unattended-Upgrade "1";
You can also check if the unattended upgrades service is running and active by running:
sudo systemctl status unattended-upgrades.service
If the status is green and active , then it it is running.
You can also run the unnattended-upgrades package on demand. To run it now, do:
sudo unattended-upgrade -d
That’s it for this Ubuntu 22.04 Autoupdates section. Feel free to check out the other options that are available for you in the auto-updates config file.
Step 12 Install HestiaCP Ubuntu 22.04
After doing this Ubuntu 22.04 Initial Server setup you can install a Web hosting Control panel.
If you want to run a PHP based web application such as WordPress, Magento, PrestaShop etc, you can use a free control panel such as HestiaCP,
What is HestiaCP?
HestiaCP is a free Web Control Panel that comes with a Web server,email server, DB server, DNS server and other tools you need to get your website online.
Hestia Control Panel is all you need if you want to start hosting WordPress or any other PHP website on a VPS.
You can install the HestiaCP components you require. This can be done by using Hestia install option flags which can be generated or if you know how to customize the settings yourself, you can do so .You may install the LEMP stack and all other apps needed for your website to run. You can generate your HestiaCP install script here or on the Hestia install page.
If you need to reset your Hestia admin user password
sudo /usr/local/hestia/bin/v-change-user-password admin mysecurepassword2020
That’s it for this Ubuntu 22.04 initial Server Setup post. If you have any question feel free to message me in the comments section below.
Tags: Ubuntu22, Ubuntu 22, Ubuntu 22.04, Ubuntu 2204, Ubuntu20, Ubuntu 20, Ubuntu 2004, Ubuntu 20.04

![Ubuntu 22.04 Initial Server Setup on VPS Cloud [Video] Ubuntu 22.04 Initial Server Setup on VPS Cloud [Video]](https://bizanosa.com/wp-content/uploads/2022/08/46-Ubuntu-2204-initial-set-up-150x150.png)
![Debian 11 Initial server setup on Cloud VPS server [Video] Debian 11 Initial server setup on Cloud VPS server [Video]](https://bizanosa.com/wp-content/uploads/2022/12/New-Debian-11-Initial-server-setup-on-Cloud-VPS-server--150x150.jpg)

